Adjusting your country selection will clear the contents of your cart.
Dell Technologies Proven Professional Knowledge Sharing Program
Annual competition has been paused until 2025
Over the past 17 years the Proven Professional program has published over 650 articles which have been downloaded over 2.5 million times. These articles continue to provide value to our audiences and the IT industry at large.
Given the significant amount of change over nearly 2 decades, and particularly with the introduction of Generative AI, we are pausing the Knowledge Sharing Competition for 2024.
We will use this gap year to evaluate how to best incorporate new technologies into the program and still allow for the sharing of best practices and cutting edge introspectives.
In the meantime, browse the Knowledge Sharing Library for some reading nuggets you may have missed.
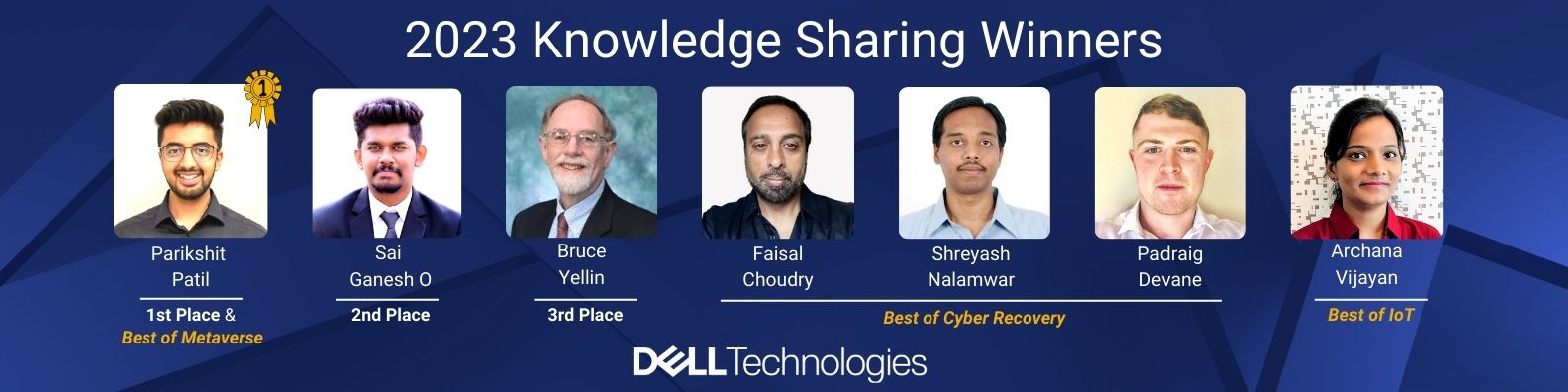
2023 Knowledge Sharing Winners Announced
Click here to watch a recording of the 2023 Knowledge Sharing Awards Ceremony.
2023 Competition First Place Winner
|
Parikshit Patil |
In this Knowledge Sharing article, awarded 1st Place in the 2023 Knowledge Sharing Competition, Parikshit Patil shares how data center technology, implemented into space missions, will completely transform multiple aspects of space exploration and research. Parikshit helps the reader understand how important space exploration is to lead a more comfortable life on Earth, not only in terms of basic requirements such as healthcare and natural disasters prevention, but also to enhance and propel our standard of living to a greater degree by means of technology and innovation. |
2023 Competition Second Place Winner |
Sai Ganesh |
IT practices, such as Cloud FinOps and GreenOps, can help organizations save money, reduce their environmental impact, and operate more sustainably. As more organizations become aware of the importance of sustainability, the adoption of FinOps and sustainable IT practices will become increasingly essential for companies to remain competitive and responsible. This article awarded 2nd Place in the 2023 Knowledge Sharing Competition; Sai details the best way to handle these considerations. |
2023 Competition Third Place Winner |
Bruce Yellin Retired Advisory Engineer |
In this Knowledge Sharing article, awarded 3rd Place in the 2023 Knowledge Sharing Competition, Bruce Yellin examines embedded systems and the miracle of the microchip. Bruce takes the reader through the digital world, where we are surrounded by embedded systems. He explores the enormous contributions they have made in society, and how these systems run nonstop with minimal human intervention and if done right, how these intelligent devices will improve our quality of life. |
Best of Metaverse
|
Parikshit Patil |
In this Knowledge Sharing article, awarded Best of Metaverse in the 2023 Knowledge Sharing Competition, Parikshit Patil shares how after decades of dreaming, imagining, and suggesting what a Metaverse could be like, it is finally within the reach of this generation. Parikshit discusses how the Metaverse will play a significant role in technology. Helping the reader understand the flexibility and change offered is limited by nothing but one's imagination. |
Best of Internet of Things
|
Archana Vijayan |
This article is an overview on how IoUT is making a positive impact in this data era. Archana shares how this ongoing concept has researchers looking for new ways to make this work even more successful. You will explore the Internet of Underwater Things (IoUT). As organizations are digitally transforming and data has become more essential than ever, digital solutions like IoT for terrestrial and aerial ecosystems and IoUT for the marine ecosystem, Big Data with intelligent Machine Learning algorithms along with Cloud-based infrastructure are incorporated for innovative and efficient transmissions. |
Best of Cyber Security
|
Faisal Choudry Shreyash Nalamwar Padraig Devane |
In this Knowledge Sharing article, awarded Best of Cyber Security in the 2023 Knowledge Sharing Competition, the authors demonstrate the different approaches needed to address a cyber-attack compared to a standard disaster event. Each solution will depend on a host of factors as discussed in this article. The authors investigate how these attacks have led to the direct involvement of governments and their agencies. In a number of these cases, new legislation has been created to help combat this threat and legislate how certain organizations operate and secure themselves. |
2023 Articles & Publication Schedule
| July | |||
| Title | Category | Author(s) | Summary |
| A guide to protecting any data on any cloud | Cloud | Pablo Calvo Services Provider Dell Technologies |
What if we could combine all the successful traditional data protection tools and practices and still maintain scalability, replication, protection and more? This article discusses how we can adapt our data protection approach to new demands, transparently, and manage a copy of the data in a universal backup platform. It will detail how we can define a “cloud-aware” layer, for a more flexible solution that can be adapted to any cloud provider. |
| AutoML for Improved Customer Churn Prediction | Artificial Intelligence | Shriya Avasthi Associate Sales Engineering Analyst Dell Technologies and Dr. Partha Sarathi Mangipudi Professor Amity Centre for Artificial Intelligence (ACAI) Amity University, Noida |
Customer retention is often more valuable than customer acquisition. The churn-rate of technical companies is historically high. Data analytics plays a critical role in predicting customer churn and understanding the latest trends and requirements for customers. This article discusses how Automated Machine Learning (AutoML) can automate the workflow of processing these datasets, for improved results and positive business impact. |
| Digital Avatars - The Future's Face | Emerging Technologies | Anjali Jayanti Associate Sales Engineer Analyst Dell Technologies Sana Kulsum Rizvi Associate Sales Engineer Analyst Dell Technologies Akarsh Raj Associate Sales Engineer Analyst Dell Technologies |
With digital avatars becoming a trendy way to represent oneself online, it may soon become the norm for Artificial Intelligence powered avatars to be used for a wide range of tasks. This article dives into what digital avatars are, how they can be created using various technologies, what they might be used for, and other advantages. It also explores what the future may have in store for these human-like creatives as the metaverse continues to evolve. |
| Modernize Data Protection with Automation | Automation | Raghava Jainoje Advisory Systems Engineer Dell Technologies Mike van der Steen Principal Systems Engineer Dell Technologies |
Automation is a key component as organizations continue their digitization journey. It has the power to optimize and reduce effort spent on manual and repetitive tasks with automation tool sets. This article details how automation can assist with data protection efforts by considering modern protocol supports, such as REST API. |
.png)